Have you had difficulty finding the mounting bracket that fits the Cisco Meraki MR42E-HW? Let Lyle Gore at Ethos Dynamics clarify the confusion surrounding the bracket part number and help you find the solution.
Have you had difficulty finding the mounting bracket that fits the Cisco Meraki MR42E-HW? Let Lyle Gore at Ethos Dynamics clarify the confusion surrounding the bracket part number and help you find the solution.
What is a Used Meraki product?
Why is Buying Refurbished Meraki Better Than Used Meraki?
When you buy refurbished Meraki from us at Ethos Dynamics, you are buying Meraki products that are renovated. When they come in the door, they are immediately checked to verify claim status in the Meraki dashboard. If unclaimed, we then check to see if the products power on correctly. During the test process, we test for port data transfer and PoE, if needed. For those items that may fall under a recall, we check their status and test for any possible failures related to the recall. For units with dual A/C option, we test both power slots. After the testing process is complete, we wipe the products down, disinfect them, and also clean them to make them look in the best shape they can possibly be in when reaching the end user. This includes: fixing dents, painting the unit in Cisco Meraki paint, clearing scratches, , and replacing screws or faceplates that are too damaged to resell. Mounting brackets on network switches are also adjusted to make functionality perfect if needed and applicable. Products are sent out bubble wrapped with secure boxes to ensure no shipping damage. Every product that we sell at Ethos Dynamics goes through this extensive process to make sure the customer is highly satisfied with our work.
Supply chain problems associated with Covid-19 shutdowns are wreaking havoc on customers looking to deploy new, or, upgrade aged Meraki networks. While the secondary market cannot overcome all issues for new deployments; having a coherent strategy working within the VAR/New order system and the secondary market has helped many companies to fill the gaps.
Many Meraki admins and MSP’s are using their traditional channels of buying new to forecast forward demands, either for their own use or their clients; and then engaging with the secondary market to fulfill immediate use requirements. By adopting this dual strategy, they are both meeting deployment times needed for current projects, and knowing that they have a plan for future ones.
The licensing aspect of Meraki dictates that networking designers and installers must take into account transferability and interconnectivity of licenses with other deployments in their network. Although, many of these are able to be managed. The paragraph below is a case in which we assisted with deployment.
Client A has 15 installations over the next 12 months at new store openings. This client is generally standardized on MX68 firewalls, MS120 series switches and wants to install 802.11ax (Wifi6) in all new facilities. With each of these families being on 3-10 month lead-time for new Meraki, we worked with them to come up with a manageable plan to meet the timetables on the most pressing installations. First, we were able to supply the firewalls and switches required, from our own stock. In the case of the WiFi6 wireless access points needed, those were not available. We worked with them to determine what they had previously standardized on for wifi, and supplied those same products refurbished to match the quantity needed. Because of the transferability of the licensing on Meraki’s MR line, when the new WiFi6 access points do become available, the licenses can be transferred with no loss of term. We then put in place a buy back plan. The plan was to take the older units back into our stock once they had their new ones deployed. This client now has a cohesive strategy for current and future deployments throughout the year.
Planning a course of action to combat unforeseen problems that arise, is the best strategy to implement at the forefront of any project.
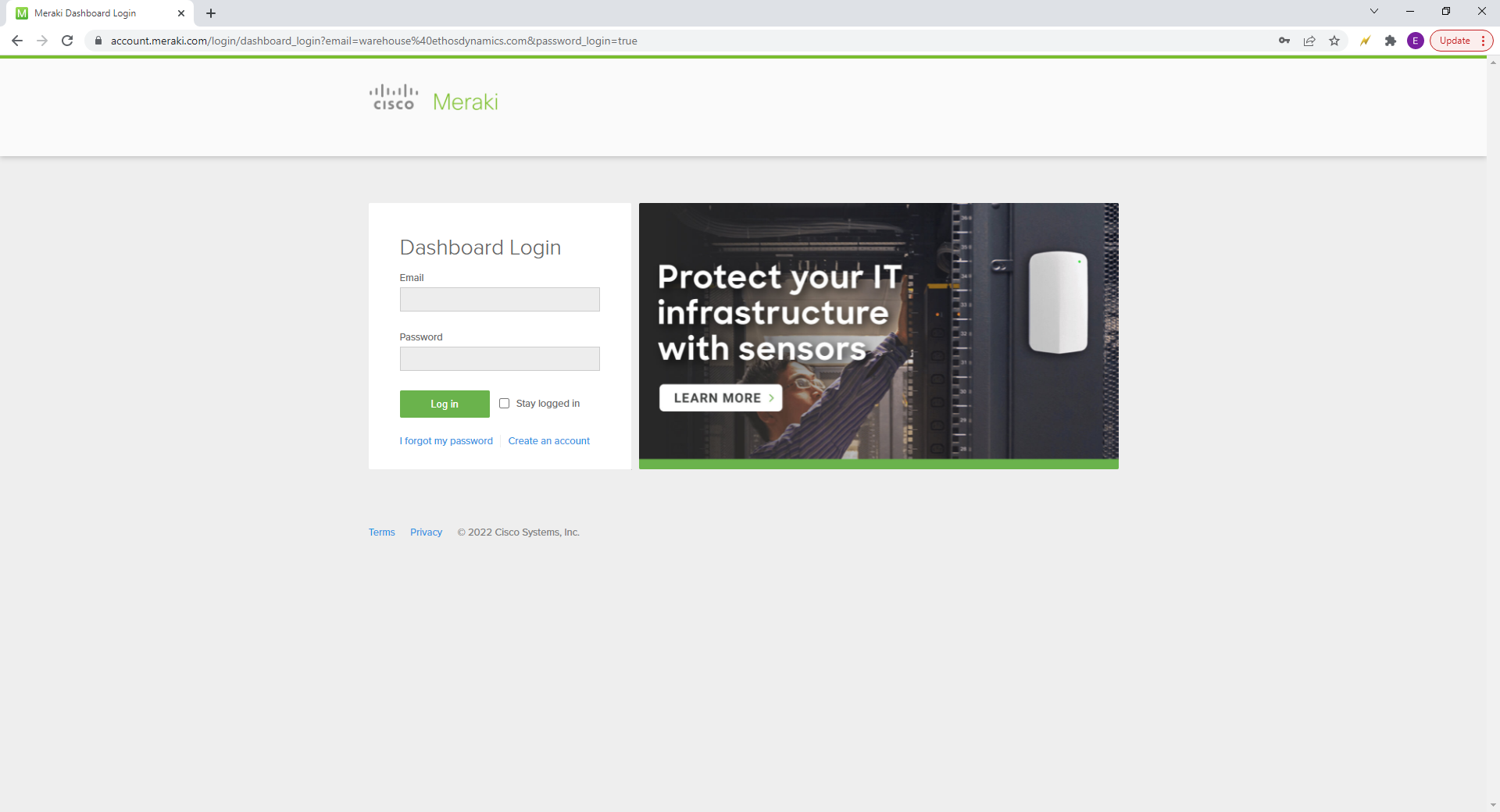
Login to the Meraki Dashboard using your credentials.
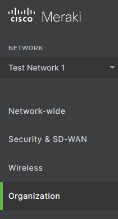
Next, hover over the Organization tab on the left side.
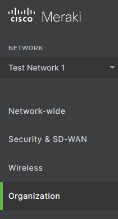
From the Organization tab, click on Inventory.
Enter SN into “Search Inventory” box.

Beside the devices Serial Number, you will see which Network the device is in.
![]()
In the top left “Network” menu, click the drop down menu and choose the same Network the device is in.


In this case, it is a Wireless Access Point, so once in the network, hover over “Wireless”, on the left side of the page.
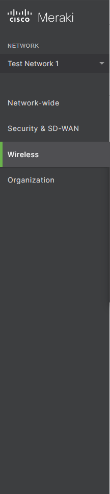
Choose Access points from the Wireless tab.
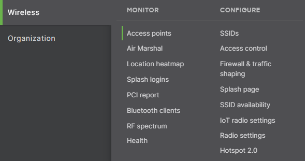
Type in the SN in the “Search” bar.
![]()
Click the check box to the left of the unit you want to remove.
![]()
![]()
Click the “Edit” button.
![]()
Choose Remove from network.
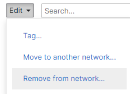
Choose Remove.
This will remove the unit from the active network.

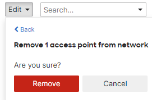
In order to fully Unclaim, hover over Organization again on the left side of the page.
Choose Inventory from the Organization tab.
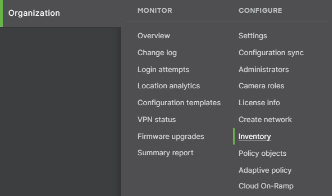
Enter SN into “Search Inventory” box.

Click the box to the left of the unit to highlight it.
Click “Unclaim”.
![]()
This will fully remove the SN from your network and organizations inventory.
The privacy of data is more important to people now, than ever. The constant breaches and hacks keep us always on edge about our information getting leaked. We need to stay as protected as we can from attacks on our network. There’s a solution to this problem. Firewalls are the best way to keep outside connections from getting in your network and also protects sensitive data in a safe place.
Firewalls are security devices that help protect you from attacks on your network. Firewalls act as an intrusion prevention system against Malaware and application-layer attacks. They react to attacks quickly and attentively to make sure your network is not affected by any malicious behavior. They also can set policies to better your network from being attacked or preyed on by processing quick assessments to detect the activity.
To put things into perspective, according to Ponemon Institutes report 66% of people have experienced a cyber-attack in the last 12-months. Of the same sample group, 45% of people say that their processes are ineffective at mitigating attacks. Malware is the most common virus that is talked about in today’s time. Malware is any piece of software that was written with the intent of doing harm to data, devices, or people. Back in 2009, 12.4 million people were infected by Malware. In 2018, the number of people infected by Malware increased to 812.67 million. This data shows that Malware has increased over 6,000% in a 9-year period. Given the statistics of these attacks happening, it’s hard to say that you won’t be targeted eventually (if you haven’t already).
If you operate with sensitive information in your business or personal life, firewalls are a must-have. Your information will be safely stored without worries. If you are looking for a firewall that suites you best, I’d recommend a Meraki firewall. At Ethos Dynamics we have Meraki Firewalls available for sale right now. Head over to our website to protect your network today, with a Meraki Firewall.
Now that you understand the wireless access point and how they work, we can discuss how they benefit your home, or business. First, they give internet connectivity to wireless based products. Second, they do not impact the internet speed, the wireless access point will not make your internet connection slower. Third, they can support many different wireless internet users on a network. Fourth, they have a broader transmission range than regular wireless routers. Wireless access points are perfect for your business. Check out our website for New and Refurbished Meraki Wireless Access Points that would be suitable for you.

From beginning to end, depend on our customer service, operations and sales team to deliver unparalleled professional and ethical service.
Latest News
 How Ethos Dynamics Receives Inventory From CustomersJuly 31, 2023 - 11:19 am
How Ethos Dynamics Receives Inventory From CustomersJuly 31, 2023 - 11:19 am What Mounting Bracket Actually Fits The Cisco Meraki MR42E-HW?January 16, 2023 - 1:52 pm
What Mounting Bracket Actually Fits The Cisco Meraki MR42E-HW?January 16, 2023 - 1:52 pm Do You Have Meraki Products That Are Not Being Used?September 1, 2022 - 10:21 am
Do You Have Meraki Products That Are Not Being Used?September 1, 2022 - 10:21 am Used Meraki Vs. Refurbished MerakiJuly 20, 2022 - 10:10 am
Used Meraki Vs. Refurbished MerakiJuly 20, 2022 - 10:10 am
Get In Touch
Address
470 Satellite Blvd. NE
Suite J
Suwanee, Ga 30024
Phone
Email us
Follow us
